It has begun! I have started to use Linux on my laptop for both work purposes and for play. I’m running a distribution or “distro” form of Linux called Mint and I must say, I AM impressed. It’s designed to feel a lot like Windows and does just about everything I need an operating systemContinue reading “MOVING to LINUX [Part 4] – “Dipping the toe””
Category Archives: Blog
Digital Hygiene [Part 3] – P@$$w0rds (passwords)
“The number one used password in 2018 was ‘123456’, which is followed by another maddeningly obvious choice, ‘password’. “
All about Podcasts
In this weeks blog post I wanted to talk about something near and dear to my heart; Podcasts. I currently have about 20 hours of podcasts queued up and ready to listen to. In fact, I need to start picking some of them to let go of so I can get through them at aContinue reading “All about Podcasts”
Digital Hygiene [Part 2] – FREE PC Protection
…today’s topic; protecting your computer from viruses and other malicious software (referred to as Malware). Now, as you might have started to guess, I like to see what I can do on the cheap, or even better, for free….
WPS Office, The Free Alternative
It’s that time again, public service announcement! I’m quite enjoying sharing with you some of my favorite free programs. It’s amazing what you can achieve with free software, oh, I forgot to mention that I found an acronym for this kind of software, FOSS (Free Open Source Software) cool eh?
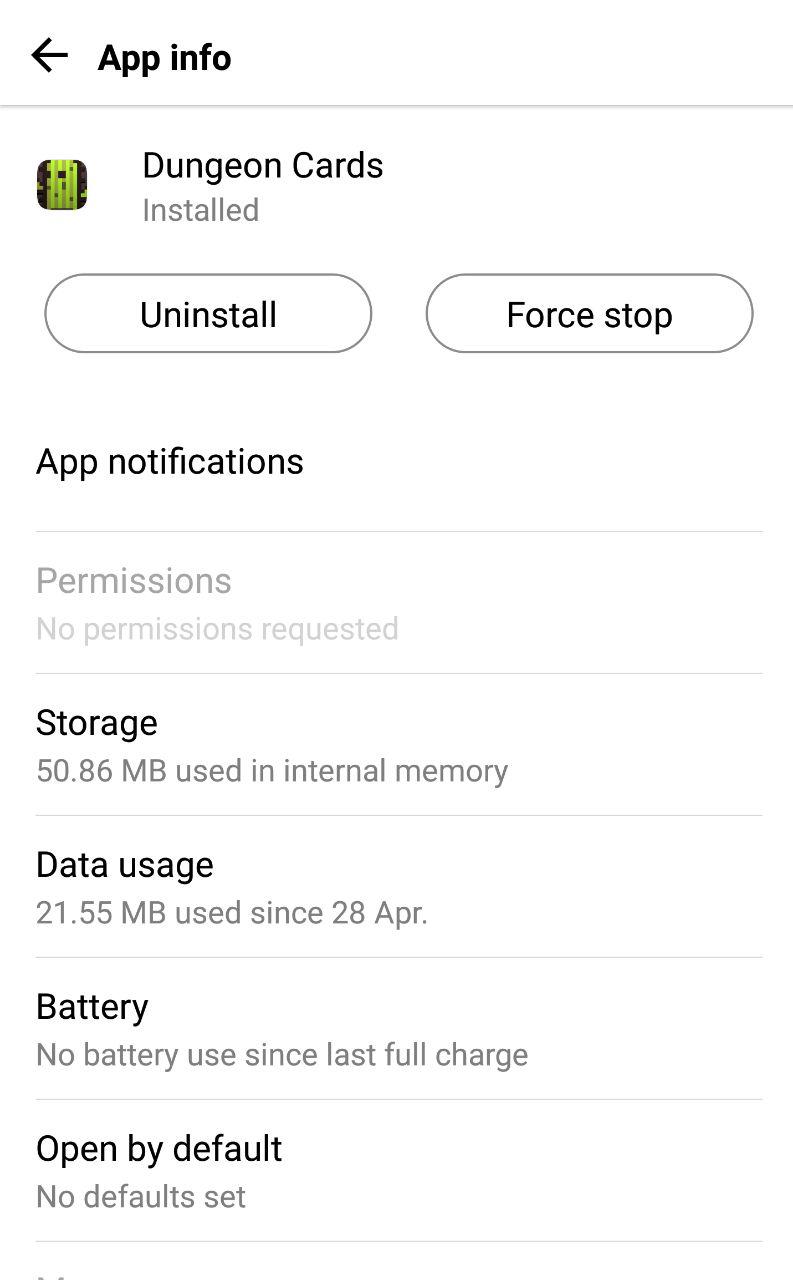
More about apps and phones
Welcome back everyone, part two here today about apps on your mobile phone and some things that will be useful to know about your phone its self. Last week we talked about the three to check with new apps (Age rating, star rating and requested permissions) as well as checking who made the app, weContinue reading “More about apps and phones”
All about Apps
We all have one, some of us have more than one. These days it seems hard to imagine NOT having one. I am, of course, talking about mobile phones. Whether it’s just to be able to contact friends and family members, or to listen to music and podcasts (I love podcasts, and yes, I’ll beContinue reading “All about Apps”
Digital Hygiene [Part 1] – “Can I borrow your toothbrush?”
Treat your password like a toothbrush. Which means you should; a) Pick a good one, b) Change it regularly and c) Never share it.
MOVING to LINUX [Part 2] – “Why I’m moving to Linux”
I wanted to just quickly touch on the key reasons why I’m moving away from Microsoft as it will become a good framing point for the continuation of this series.
How to be Brave
The first question you might have is “Well why would I use brave instead of Google Chrome?” the simple answer is that Brave is designed to block all of the “nasties” straight out of the box.